Contributing Authors: Eric Celidonio and Lauren E. Perna
Marc was the perfect candidate for a principal scientist job that we were having a difficult time filling. On paper, he was a well-qualified molecular biologist with degrees from top universities and impressive biochemistry skills. When our lead recruiter reached out to him, he played hard to get, but after a couple of attempts, he agreed to come in for an onsite interview.
Marc acted strangely during his interview–he was more interested in the facility than the actual job, frequently glanced around at his surroundings, and he asked a number of questions not related to the role. Marc also requested a tour of the lab, which was provided by a junior team member. By the end of the interview, it was clear that he wasn’t a fit for the role. In fact, despite his impressive credentials on paper, he didn’t seem to have any transferable skills or interest in the role.
While most of the interviewers chalked up Marc’s strange demeanor to just being a poor candidate for the job, it turns out that Marc wasn’t there for a new job. He was using the interview process to access intellectual property for a foreign competitor.
Marc used the opportunity to gain access to key, confidential information. He even stole a couple of USB drives as well as documentation when he was left alone in an interviewer’s office and when he walked unescorted to the restroom. He also brought an inexpensive pen camera with a microphone to record the discussion, effectively delivering accurate, sensitive detail with minimal effort.
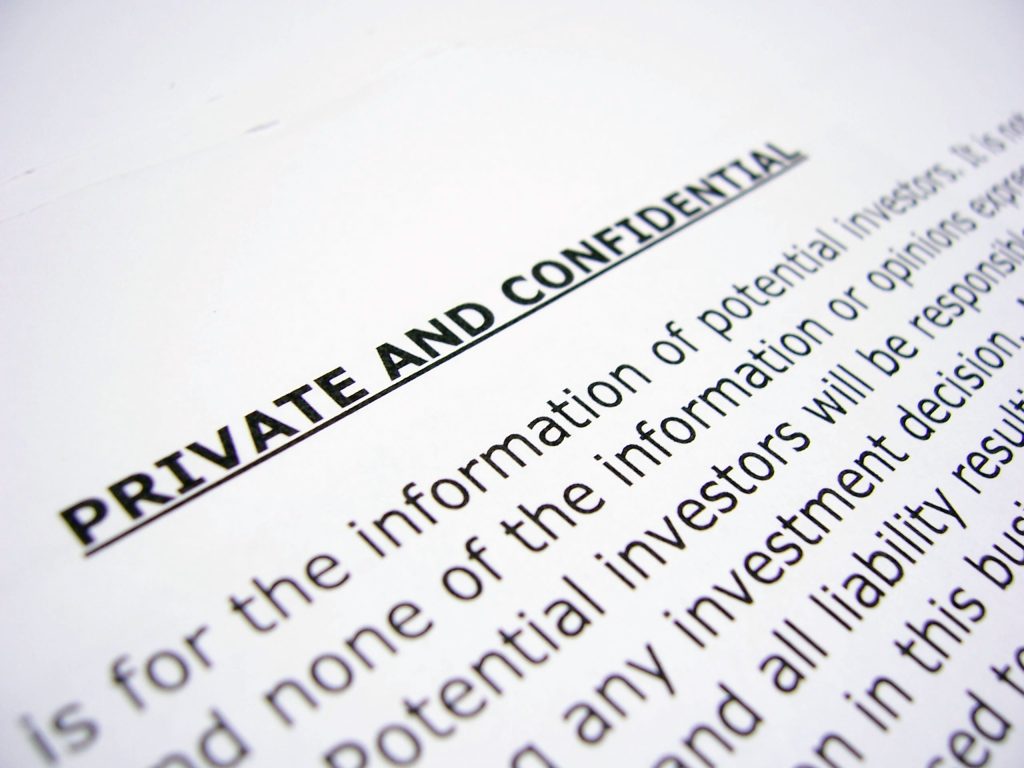
Intellectual property (IP) theft via corporate espionage, also called industrial espionage, involves the theft of data meant for economic gain. This type of spying occurs between companies, corporations, and sometimes foreign governments. The candidate interview process creates a unique opportunity for these transgressions. Many interviewers might not even notice a stealth candidate taking a picture of a confidential whiteboard, stealing a USB drive, or taking a sensitive document left on a common printer.
Marc had signed a confidential disclosure agreement (CDA), meaning that he had agreed not to share the information learned in the interview with others. So the interviewers thought it was perfectly fine to share confidential information with him. By the end of the interview, Marc knew platform secrets, what compounds were being investigated, and what programs were being advanced. The CDA he had signed was meaningless–he provided the “lifted” information to an officer at a direct competitor outside the U.S.
Corporate Espionage: A Very Real and Expensive Threat
Corporate espionage can take many forms and can have a devastating impact on a company. While it is outlawed by the Economic Espionage Act of 1996, unfortunately, it’s still a relatively common practice. Some companies manage to spy on their competitors under the radar. The reverse situation of the one we encountered can also happen–an unsuspecting employee goes to a competing entity and is interviewed on the basis of “leaking” proprietary or sensitive information. Many corporate spies do not get caught or are caught after it’s too late and the intellectual property has been transferred.
According to the U.S. Commission on Theft of American Intellectual Property, the annual cost to the U.S. economy is on the order of hundreds of billions of dollars. This cost continues to exceed $225 billion and could be as high as $600 billion to U.S. corporations. Life science companies are some of the hottest targets. China alone has stolen IP from one in five US companies in 2019 according to a CNBC Poll.
This high cost includes not only lost IP but also financial information, marketing strategies, projects in development, pricing, and employee personal information. In addition to a potential competitive setback, such losses can additionally tarnish a company’s reputation as a leader and an innovator. Biotech is uniquely susceptible to espionage due to its fast pace, frequent directional change, and often poorly governed processes.
Now that we’ve told our real-life tale of a biotechnology spy, in the next section we’ll review other ways companies could open themselves up for IP theft.